The Android platform is currently the top selling mobile platform in the U.S., and in quarter four of 2010 smartphones began to outsell PC platforms worldwide. Android was even recently picked up as the choice platform for the U.S. Department of Defense. With the ubiquitousness of Android growing, naturally it and other smartphone platforms will become prime targets for malware authors. Be it for fun or for profit, stealing your information, sending you spam, and other malicious activity, has been a widespread problem in the computing world for years. It is only natural that as smartphones know even more about their users than traditional PC platforms, and have access to additional features such as text messaging and GPS data, that they will be become juicy targets for high tech criminals.
This past year has seen new developments in Android malware both in the wild and by researchers intent on raising awareness and improving the state of security. The Droid Dream attack against Android in early 2011 made headlines for being the first known malware infection inside of the official Android market. The malware was packaged with seemingly legitimate applications, but once installed, the apps turned Android phones into drones in a mobile botnet. This attack had been foreshadowed by security researchers when Jon Oberheide uploaded a proof of concept app to the Android market disguised as an inside look at the upcoming Twilight movie. Though malware analysists and network security experts have been combating botnets for years, smartphones open new avenues of both attack and control, that experts simply don’t have as much experience analyzing. For example security researchers have created proof of concept smartphone botnet scenarios that use text messaging (SMS) for command and control mechanisms.
Putting aside the continually growing sophistication of smartphone based attacks, how easy is it actually to attack Android phones? How much work would be involved to learn how to write an Android app, develop an app that performs malicious activity, and get that app up on the Android market? Is this something that a beginner could feasibly accomplish, or is Android malware solely the realm of hard core criminals with the skills, time, and money to develop cutting edge attack techniques?
I started off by learning a little bit about coding in Android. I have some coding background including in Java, the language from which the Android software development kit was derived. My only previous experience developing for smartphones was writing base operating system level proof of concept malware in C. I had never written a mobile app before. Android Developer offers beginning tutorials, which I worked through to get started. Android prides itself on being easy for developers to pick up and dive into, and that was my experience as well.
My next goal was to write an app that performs malicious activity. Specifically I wanted to steal the smartphones personal identifier (IMEI) and send a text message without giving any indication to the user. As it turns out the Android API has built in capabilities to perform both of those tasks. The only caveat is the user has to be informed at install time that I want access to these clearly potentially dangerous capabilities. Whenever a user installs an Android app, they are presented with a list of potentially dangerous capabilities the app requests. An example install screen is shown below:
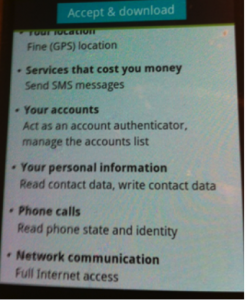
I then wondered if malware writers need to somehow bypass this permission model in some way so the dangerous permissions don’t show up at install. Would having a list of dangerous permissions that would allow an app to steal data and run up fraudulent charges raise a red flag to average Android users and deter them from installing an app? I did a search for popular Android apps to take a look at the permissions they request. The general consensus seems to be that the top downloaded Android app of all time is from an obscure company called Facebook. The complete list of permissions the Facebook for Android app requests upon install includes: sending SMS, reading the IMEI, the smartphone’s GPS information, accessing accounts stored on the phone including their credentials, among a long list of others that can be found here. As a sometimes proud member of Facebook since it was for college kids only, I often access Facebook from my computer. Facebook seems to work just fine without sending SMS, knowing my location, or having access to my Gmail password. It appears that being warned about potentially dangerous permissions does nothing to deter users from installing apps to their Androids. To be fair, the Facebook app comes from a legitimate and well known company. Users have less reason to be wary of Facebook than they would the sort of apps seen in the DroidDream attack. That being said, as we saw in the recent detection of spyware in the CarrierIQ service installed by default on many smartphone platforms, any service or app can be a potential malware source, even if the developer doesn’t intend for it to be malicious.
Now that I knew I could just use the Android API’s permission model to make my malicious app, I went about writing it. I thought I would have to search through the Android Development manager to find out the correct code for what I wanted to do. As it turned out, a quick Google search for “Send SMS Android App” or “Access IMEI Android App” revealed several other curious developers asking for and providing the code snippets I needed. For example the code to send an SMS transparently to the user is only a two lines long:
SmsManager sm = SmsManager.getDefault();
sm.sendTextMessage(number, null, message, null, null);
where number is the phone number to send the SMS to, and message is the message to send. By requesting the right permissions I was able to quickly and easily build an app that accessed private data and sent it to another phone through SMS. The SMS does not appear in the user’s sent folder, so users receive no indication that the message has been sent.
My demo app in action video:
My last task was to see about getting my proof of concept app to the Android market. Using a Gmail account that didn’t link back to my real name I was able to sign up, and I used someone else’s credit card (with permission) to sign up. This leads me to believe it is possible for a malware author to leave no trace of her true identity on an app. I didn’t actually publish my app to the market, but other researchers have already proven that a malicious app is automatically published to the Android market upon upload.
My conclusions are that for anyone with any development experience it is easy to pick up the Android programming language. Thus any malware authors with experience on PC platforms will be able to make the switch to Android without any trouble. Also, the Android permission system is not working to keep users safe. The average, security unaware user will often simply install an app regardless of permissions. Using the API to call malicious functionality was straightforward given the correct permissions. Finally, uploading a malicious app to the Android market is trivial.
Read more about Georgia Weidman

Sorry, comments are closed for this post.